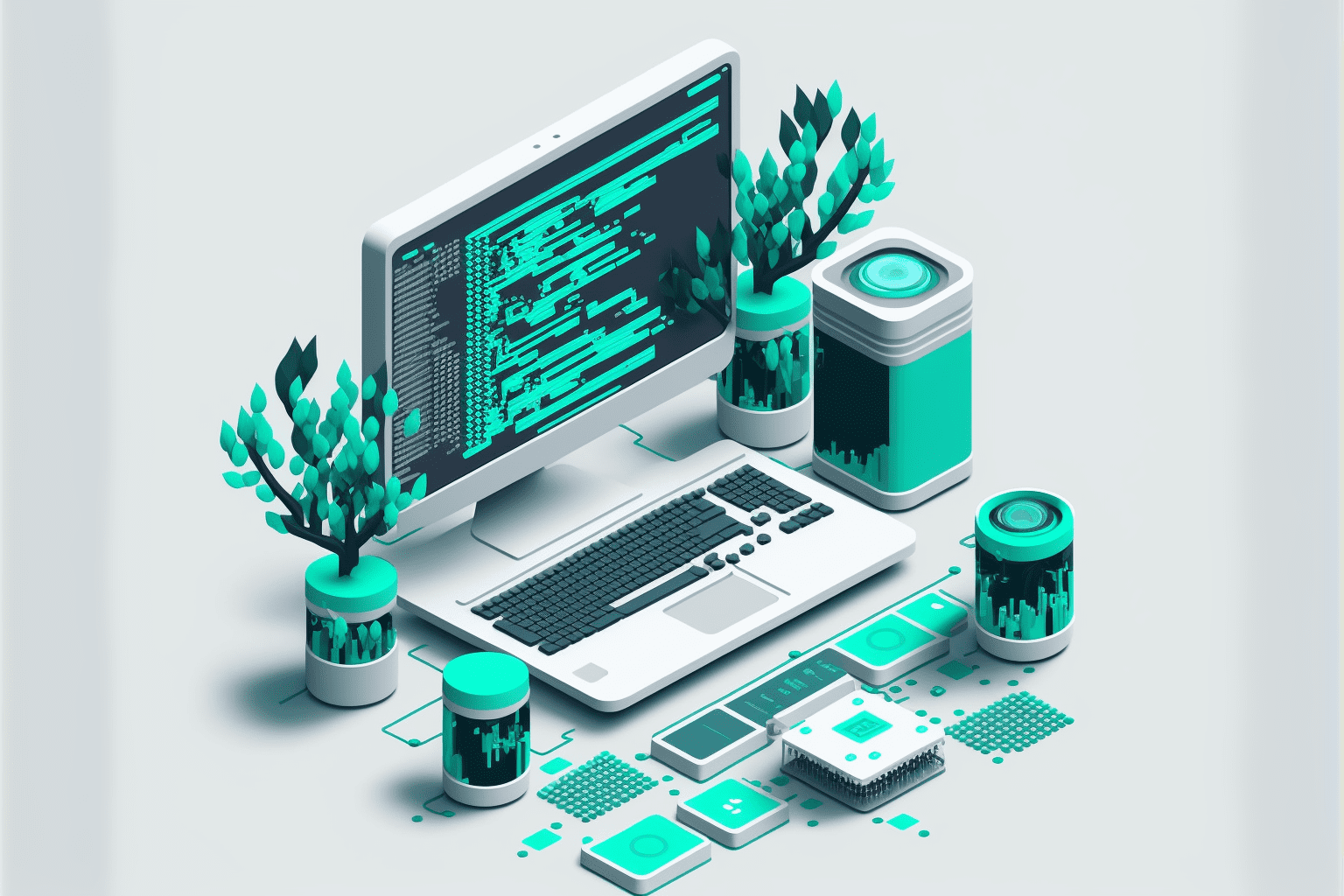
Green IT & Sustainability: CloudTech’s Approach for Birmingham Businesses
Birmingham businesses can cut costs and boost sustainability with Green IT. CloudTech’s energy-efficient solutions reduce carbon footprints, ensure compliance, and enhance reputation through eco-friendly, future-ready IT practices.